November
21
#FraudWeek: 6 Cyber Risk Trends You Need to Know Right Now (HSB BI&I Insights)
Does faster, wider and smarter actually mean safer?
While today’s digital transformation is creating tremendous opportunities, the flipside is inherent risk. Our cyber experts outline six major trends.
1. Your new computer system may already be infected
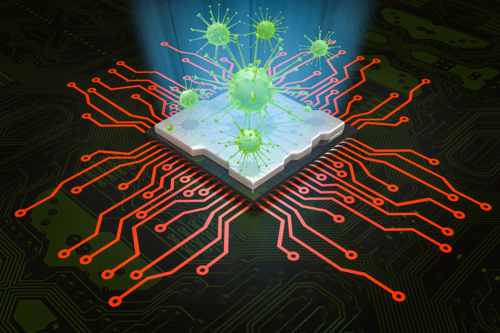
Infected chips can be inserted into hardware at any point of the computer manufacturer’s supply chain, and malware can be implanted during production of legitimate software updates.
Criminals are seeking out new and advanced ways to infect software and hardware along the entire production and distribution sequence of computer systems and software.
Most notable are scenarios in which malware is implanted into legitimate software programs and updates. Injection of malware could occur during production at the software vendor or at a 3rd party supplier, involving compromised chips or added source code to firmware.
2. Your CPU could be cryptojacked

Cryptojackers secretly use your computer’s CPU to mine cryptocurrencies elsewhere, slowing down processing power, causing overheating, downtime and lost productivity.
Cryptojacking can be a very attractive technique for hackers since it is more accessible to implement than other methods: setup is quick, it is harder to track than ransomware, and it usually provides a bigger payoff.
3. Cybercrime syndicates are unleashing stronger and more sophisticated attacks

Criminals are starting to use a combination of traditional and mobile ransomware hacks, combined with different threats used in tandem, such as a combination of phishing, ransomware and cryptojacking.
They are also becoming more patient, watching and waiting, unleashing less frequent attacks with higher impacts.
At the same time, the cybercriminal underworld is becoming more collaborative and is consolidating, creating fewer but stronger malware-as-a-service families which could lead to major disruptions and losses.
4. 5G is vaster, amplifying cyber exposures

5G has 10 times the data capacity of 4G (LTE), creating a vaster surface area over which cyber attacks can take place.
The mobile communications standard of 4G (LTE), with a data capacity of 1 gigabyte per second (Gbps) is being phased out. This is making way for the incredible leap to the 10 Gbps capabilities of the 5G network.
5G exponential growth and the resulting data explosion over the next year will result in a vast surface area over which cyber-attacks can take place.
IoT devices will connect directly to the 5G network and bypass the central router, making them more difficult to monitor and more vulnerable to direct attacks.
5. Explosion of connected devices threatens your data security

Billions of devices are now ‘always on’, exchanging data with the cloud and each other. One weak link can open up massive vulnerabilities for millions of devices on a single network.
The collaboration of mobile devices, voice-controlled digital assistants, unprecedented data collection and the delivery of cloud computing resources is bringing interconnectedness to a whole new level.
With this progress comes higher levels of complexity and increases in unsecured data exchange like never before. The vast network of devices and data transfer means that the origin of data leakage points is becoming more difficult to trace.
6. Canadian data breach laws are now in effect

Data breach notification laws are now in force in Canada, making it mandatory for all organizations to notify affected individuals and the Privacy Commissioner of any security breach.
For more information about Canadian data breach regulations, click here.
For more information about Peace Hills' CyberOne® coverage click here, and here for information about our Data Compromise coverage.
Author: The Boiler Inspection and Insurance Company of Canada (BI&I).
All rights reserved. This article is for informational purposes only and is not intended to convey or constitute legal advice. BI&I makes no warranties or representations as to the accuracy or completeness of the content herein. Under no circumstances shall BI&I or any party involved in creating or delivering this article be liable to you for any loss or damage that results from the use of the information contained herein. Except as otherwise expressly permitted by BI&I in writing, no portion of this article may be reproduced, copied, or distributed in any way. This article does not modify or invalidate any of the provisions, exclusions, terms or conditions of the applicable policy and endorsements. For specific terms and conditions, please refer to the applicable insurance form.